Rust is a low-level language with high-level ergonomics. It’s fast and reliable and supports asynchronous I/O arriving in stable Rust. As such, Rust is quickly becoming the premier choice for performance-focused network and web applications.

Virtually all web apps require some form of authentication, especially in an age of ever-increasing awareness around data privacy. Rust has a wide and growing range of high-quality, production-ready crates available for authentication and authorization.
In this guide, we’ll evaluate nine stable, production-ready authentication libraries based on the following criteria:
We’ll also preview some crates that aren’t yet production-ready but should be on your radar.
Let’s dive in!
cookiecookie is a crate for creating and parsing HTTP cookies. It’s used for managing sessions, encrypting, and signing cookies.
cookie is a production-ready crate with thousands of downloads. It serves as a foundation for building session-based authentication strategies. The crate supports saving and recording changes in cookies. It’s web framework-agnostic and supports actix, rocket, and all other frameworks.
jsonwebtokenJSON Web Tokens are very popular for authorization; many OAuth provider issues JWT. jsonwebtoken provides support for verifying and creating JWT tokens.
The crate supports all standard signing algorithms as well as both symmetric and asymmetric encryption algorithms. It comes with built-in validation of standard claims and strongly typed and highly configurable APIs. It also features full implementation of RFC 7519.
jsonwebtoken is a highly stable and widely used library with thousands of downloads. Best of all, it has an active team of maintainers with huge community support.
oauth2oauth2 provides a complete implementation of the OAuth 2 protocol. It supports async and sync I/O, obtaining access tokens, verifying state, and obtaining refresh tokens.
Features include full implementation of RFC 6749 and strongly typed. The crate has support for state and crf_state validation as well as PKCE challenge. Furthermore, a custom HTTP client with default support for reqwest and curl is baked into the crate.
Finally, oauth2 is framework-agnostic and supports using a password and username directly.
Examples of other oAuth providers include:
oauth2 is easy to use and provides a complete OAuth 2 client solution, including refresh tokens, managing claims, scopes, and grants.
otpauthotpauth provides support for both HOTP and TOTP algorithms. It’s used to generate one-time passwords (OTPs). It can generate time-based OTPs with support for changing validation time.
otpauth‘s APIs are easy to use and intuitive, and it features full impementation of HOTP and TOTP.
yup-oauth2yup-oauth2 provides the implementation of OAuth 2.0 for server-to-server. It’s used to implement a client library for different services, such as google-api-rs.
The crate supports both service accounts and installed applications and works with any service that implements OAuth 2.0 for server-to-server authentication. yup-ouath is typically used for authentication on devices with limited input capabilities using device flow. It’s used in services such as Google cloud platform, Firebase, and other Google services using service flow. It also supports application where the authentication token cannot be saved securely using installed application flow.
ASAP is an authentication mechanism created and maintained by Atlassian. It supports nonstandard claims and performs validation and token generation at lightning-fast speed.
ASAP is based on the jsonwebtoken crate. It fully supports ASAP specifications.
JWKS-Client provides support for validating JSON web tokens using a JWKS (JSON web keyset). The primary function of the crate is symmetric signature validation for JWT tokens using a JWKS.
The crate is primarily used for Google and Firebase OAuth but can be used with any other provider easily. It takes the URL of the key arguments and verifies the token. It also supports key caching.
opensslThe openssl crate is Rust binding for the OpenSSL library. It provides full support for signing tokens, hashing passwords, generating random auth tokens, and encrypting data.
Many authentication libraries use OpenSSL for signing and hashing data. jsonwebtoken uses OpenSSL for signing tokens.
The openssl crate has support for both static and dynamic linking. It also supports the available version of OpenSSL or downloads the required version.
pgenpgen generates passphrases using the EFF’s wordlists for random passphrases.
The following libraries are not yet stable but have promising features and should be on your radar. As Rust grows, it will support more and more standards.
boringauthboringauth is a one-stop solution for any app’s authentication-related needs. It supports passpharse authentication and both HTOP- and TOP-based authentication. It also features a customizable period, hashing algorithm, output length, and initial timestamps.
boringauth can be used in CLI and desktop apps. It doesn’t have full support for HTOP and TOPT just yet. Suport for universal two-factor authentication is also forthcoming.
oxide-authThe oxide-auth crate provides implementation of OAuth for the server. It has support for many web frameworks, including Actix, Iron, Rocket, and Rouille.
Put simply, oxide-auth makes managing OAuth tokens on the server easy. It also supports handling token for custom servers.
Though its APIs aren’t stable yet, oxide-auth is a solid library. Support crates for web frameworks are still works in progress.
Frank JWT is used for verifying and generating JWT. It can read keys automatically from path.
This crate is not yet production-ready since it doesn’t support validation of iss , sub, and many other claims.
To summarize, below is a comprehensive table to help you compare the features, capabilities, and pros and cons of the Rust authentication libraries discussed in this guide.
| Name | Production-ready? | Type | Async support? | Primary use(s) | Drawbacks | Benefits | Maintained? |
cookie |
Yes | Helper | No |
|
|
|
Yes |
oauth2 |
Yes | OAuth support | Yes |
|
|
|
Yes |
oauth-client |
No | OAuth support | No |
|
|
No |
|
oauth-client-async |
No | OAuth support | Yes |
|
|
No |
|
oxide-auth |
No | OAuth server | Yes |
|
|
Yes |
|
inth-oauth2 |
No | OAuth server | Yes |
|
|
No |
|
yup-oauth2 |
Yes | OAuth server | Yes |
|
|
|
Yes |
| Frank JWT | No | JWT helper | No |
|
|
|
Yes |
jsonwebtoken |
Yes | JWT helper | No |
|
|
|
Yes |
otpauth |
Yes | OTP auth | No |
|
|
|
Yes |
boringauth |
No | OTP auth | No |
|
|
|
Yes |
| ASAP | Yes | ASAP auth | Yes |
|
|
|
Yes |
| JWKS-Client | Yes | JWT auth middleware | Yes |
|
|
|
Yes |
openssl |
Yes | Cryptography | No |
|
|
Yes | |
pgen |
Yes | Paraphrases generator | No |
|
|
Yes |
Debugging Rust applications can be difficult, especially when users experience issues that are hard to reproduce. If you’re interested in monitoring and tracking the performance of your Rust apps, automatically surfacing errors, and tracking slow network requests and load time, try LogRocket.
LogRocket lets you replay user sessions, eliminating guesswork around why bugs happen by showing exactly what users experienced. It captures console logs, errors, network requests, and pixel-perfect DOM recordings — compatible with all frameworks.
LogRocket's Galileo AI watches sessions for you, instantly identifying and explaining user struggles with automated monitoring of your entire product experience.
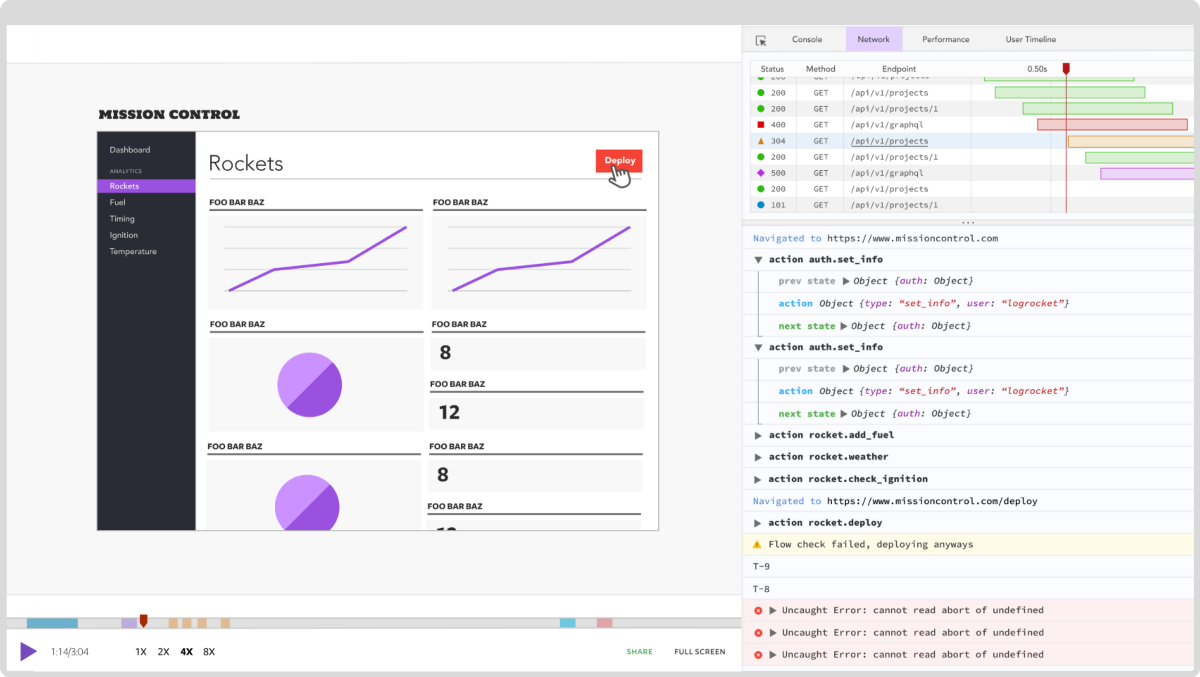
Modernize how you debug your Rust apps — start monitoring for free.
Hey there, want to help make our blog better?
Join LogRocket’s Content Advisory Board. You’ll help inform the type of content we create and get access to exclusive meetups, social accreditation, and swag.
Sign up now
Learn how to integrate MediaPipe’s Tasks API into a React app for fast, in-browser object detection using your webcam.

Integrating AI into modern frontend apps can be messy. This tutorial shows how the Vercel AI SDK simplifies it all, with streaming, multimodal input, and generative UI.

Interviewing for a software engineering role? Hear from a senior dev leader on what he looks for in candidates, and how to prepare yourself.

Set up real-time video streaming in Next.js using HLS.js and alternatives, exploring integration, adaptive streaming, and token-based authentication.